Status Dashboard ↓
R E L I A B I L I T Y
Status Dashboard
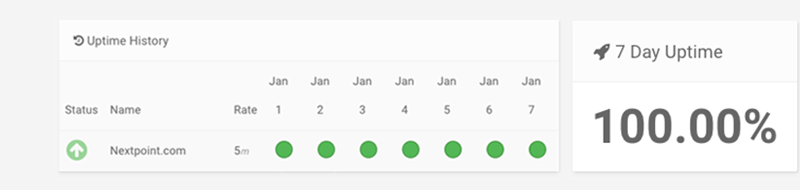
Nextpoint publishes up to the minute status information via immediate/automated tracking service at status.nextpoint.com. Additionally, incident reports will be provided for any notable service interruption.
Backups ↓
R E L I A B I L I T Y
Backups and Disaster Security
Data stored by Nextpoint is redundantly stored in multiple physical locations at no additional charge. Additional precautionary measures are also available to all customers. Customers can export and download data at any point on an unlimited basis (no additional charge) as well as elect to have data periodically downloaded and sent to them on physical media (additional charge).
Nextpoint products hosted by Amazon Web Services are designed to provide 99.999999999% durability of objects over a given year. This durability level corresponds to an average annual expected loss of 0.000000001% of objects. For example, if you store 10,000 objects using Nextpoint, you can on average expect to incur a loss of a single object once every 10,000,000 years.
Amazon S3 redundantly stores your objects on multiple devices across multiple facilities in an Amazon S3 Region (US/East-1). When processing a request to store data, the service will redundantly store your object across multiple facilities before returning SUCCESS. Amazon S3 also regularly verifies the integrity of Nextpoint data using checksums.
Nextpoint is fully prepared for complete data recovery and an immediate return to service following an accident or disaster. Nextpoint data hosted on Amazon S3 is designed to sustain the concurrent loss of data in two facilities. In the event that two facilities go down, devices in a tertiary facility are activated and data is restored with no downtime.
Physical Security ↓
S E C U R I T Y
Physical Security
Nextpoint data stored by Amazon Web Services is hosted in nondescript data centers. Critical facilities have extensive setback and military grade perimeter control berms as well as natural boundary protection.
Physical access is strictly controlled both at the perimeter and building ingress points by professional security staff. State-of-the-art video surveillance and intrusion detection systems ensure security.
Authorized staff must pass two-factor authentication no fewer than three times to access data center floors. Data center access and information are provided only to employees who have a legitimate business need for such privileges. Access is immediately revoked for employees who no longer need it, even if they continue to be employed by the company. All visitors and contractors are required to present identification upon signing in and are accompanied at all times by authorized staff. All physical and electronic access to data centers by employees is logged and audited routinely.
Client data stored at the Nextpoint office is secured in a keyed office, in a keyed building, with a security system. Server access is password protected and granted only via secure VPN.
Employee Training ↓
S E C U R I T Y
Employee Training
All new hires undergo background checks before formally starting work as well as security training as part of the Nextpoint onboarding process. Following successful completion of the training, employees sign a confidentiality agreement regarding the protection of client information. Additionally, all employees, regardless of tenure, participate in annual security training. Third-party business associates must sign agreements that include rules and responsibilities regarding confidentiality and security.Internal Audits ↓
S E C U R I T Y
Internal Audits
Nextpoint’s Site Reliability Engineering Team assesses security risks on an ongoing basis, including by running a weekly vulnerability scan. For additional assurance, Nextpoint’s Operations group meets on a monthly basis to review controls and ensure they’re operating as designed.
Nextpoint’s Site Reliability Engineering Team monitors access and audits access logs, addresses known incidents, and applies security patches. The officer also conducts a comprehensive IT risk assessment on an annual basis.
Lastly, Nextpoint employs an enterprise Secure Software Development Life Cycle (SDLC) as part of its ongoing commitment to building and maintaining secure applications. All Nextpoint applications are developed, deployed, managed, and enhanced internally.
Data Access ↓
S E C U R I T Y
Data Access
All employee data access is documented via a documentation trail. This trail includes both documentation of the request and the granting of that request by an authorized party. Only a subset of employees have access to the Nextpoint application. Other employees can view account usage summaries but have no access to lower-level client data. Access is promptly revoked for employees who no longer need it, whether or not they continue to be employed by Nextpoint.
Single-sign on and multi-factor authentication further guard against unauthorized access. Single sign-on (SSO) enables a single login for Nextpoint and other platforms, enhancing security and simplifying daily operations. It gives your IT administrators more control in defining security standards and managing access to data.
Data Encryption ↓
Data Encryption + Secure Data Loading
Data is encrypted both at rest and in storage. Data processing takes place on virtual machines explicitly provisioned to serve only one client per lifetime. Additionally, a separate MySQL database is generated and utilized for each Nextpoint database created.
Nextpoint is continuously audited to ensure it meets the high standards of SOC II Type 2, a security certification that assesses the data management of both human and computer data handlers.
AWS Cloud ↓
S E C U R I T Y
AWS Cloud Security
Nextpoint products are deployed through Amazon Web Services. Amazon has invested billions of dollars in internet technologies to ensure that Amazon Web Services is the fastest, most reliable, and most secure data host. Amazon Web Services far surpasses even the strictest privacy and security standards, including standards held by the United States Department of Defense. Simply put, there is no more secure and dependable service for storing electronic data.
Among the Amazon Web Services utilized by Nextpoint are several services specifically engineered to support secure infrastructure and applications. These include CloudWatch, used to monitor and warn of unusual system activity; virtual private cloud, used to fortify environment security; and Identity and Access Management, used to restrict Nextpoint employee access to client data as well as facilitate highly secure data uploading.
Access to the Amazon Web Services environment is restricted by IP address and blocked after five failed attempts.
Standards ↓
Security Standards
Amazon Web Services is compliant with the strictest and most comprehensive security standards available. Additionally, Nextpoint is SOC II Type 2 certified. We closely monitor changes in standards to maintain compliance.

ISO 9001, 27001, 27017, 27018

PCI DSS Level 1
CJIS
FIPS

NIST

Cyber Essentials Plus
SOC 1-3
G-Cloud

SOC II Type 2
Incident Response ↓
S E C U R I T Y
Incident Response & Breach Notification
Nextpoint’s Site Reliability Engineering Team reviews firewall notifications and operating system event logs on a daily basis. The team also monitors access levels to secured technologies (AWS, the network, the application, etc.) and failed login attempts to the application.
If Nextpoint discovers there may have been an incident in security which has or may have resulted in unauthorized access to Nextpoint protected data, we notify potentially affected users as soon as it’s possible to do so without compromising any investigation or remediation of the breach.
Nextpoint will reasonably cooperate with users in handling of the matter, including, without limitation, (i) assisting with any investigation; (ii) providing users with physical access to Nextpoint facilities and operations affected; (iii) facilitating interviews with Nextpoint employees and others involved in the matter; and (iv) making available all relevant records, logs, files, data reporting and other materials required to comply with applicable law, regulation, or industry standards.
The user shall have the sole right to determine (i) whether notice of the breach is to be provided to any individuals, regulators, law enforcement agencies, consumer reporting agencies or others as required by law or regulation and (ii) the contents of such notice, whether any type of remediation may be offered to affected persons, and the nature and extent of any such remediation.
Privacy Section ↓
P R I V A C Y
Nextpoint Privacy Policy
We have no higher priority than the privacy and security of our clients’ data. We seek to lead the industry as a trusted repository for customer data through a robust privacy program and secure infrastructure that enable our customers to comply with global privacy and data protection regulations.
CREDIT CARD DATA
Nextpoint uses a third-party intermediary, QuickBooks Payments, to manage credit card processing. This intermediary is not permitted to store, retain, or use billing information except for the sole purpose of credit card processing on Nextpoint’s behalf.
COOKIES
Nextpoint uses cookies to make interactions with our website easy and meaningful. Each time you log in to Nextpoint, a session cookie containing an encrypted, unique identifier is placed in your browser. These session cookies allow Nextpoint to uniquely identify you when you are logged in and to process your online transactions and requests. Session cookies are required to use Nextpoint. Nextpoint also occasionally uses third-party cookies. For information on third-party cookies, please see the privacy policy in full.
GDPR
The GDPR protect personal information of EU residents and citizens, including citizens residing outside the EU. By default, Nextpoint takes the overly cautious position of assuming customer data is highly sensitive. While we provide the technology to search and compile your data, we do not examine the data itself. Nextpoint also provides customers with the ability to modify and delete data in order to facilitate customer compliance with GDPR. It is customers’ responsibility to review court rules around case data before modifying or deleting that data.
PRIVACY SHIELD
The Privacy Shield is a framework for transferring personal data between the EU, Switzerland, and the US. The framework is jointly reviewed on an annual basis by the European Commission and the U.S. Department of Commerce. Nextpoint uses Amazon Web Services as its cloud security provider, and Amazon Web Services is fully certified under the EU-US Privacy Shield.
ADDITIONAL PRIVACY REGULATIONS
In addition to strictly adhering to the GDPR, Nextpoint adheres to numerous other privacy regulations by hosting data with Amazon Web Services, which complies with the strongest regulations in effect worldwide.
DATA EXPORT & DESTRUCTION
Customers can export and download data at any point and on an unlimited basis. Additionally, Nextpoint will delete customer data upon request. Nextpoint uses hosting providers that follow hardware protocols identified in DoD 5220.22-M (“National Industrial Security Program Operating Manual”) or NIST 800-88 (“Guidelines for Media Sanitization”) to destroy data as part of the decommissioning process. If a hardware device is unable to be decommissioned using these procedures, the device will be degaussed or physically destroyed in accordance with industry-standard practices.



